Cybersecurity SEO is the practice of optimizing a cybersecurity company's digital presence so that security-conscious buyers find, trust, and convert through organic search. Unlike standard B2B SEO, it demands technical accuracy, regulatory awareness, and content that serves both CISOs and non-technical decision-makers. With global information security spending projected to hit $240 billion in 2026, the buyers behind that budget are researching solutions through search and AI engines before they ever speak to a sales rep. These six strategies help cybersecurity companies turn search visibility into qualified pipeline.
Why Cybersecurity SEO Is Different from Standard B2B SEO
This table matters because cybersecurity companies that apply generic SEO playbooks miss the nuances that actually drive qualified pipeline. The strategies below address each of these differences.
1. How Does Simplifying Cybersecurity Jargon Improve SEO and Conversion Rates?
Cybersecurity SEO starts with a fundamental content challenge: your buyers range from CISOs who think in MITRE ATT&CK frameworks to VPs of Marketing who need to justify security budgets to their board. Creating a comprehensive glossary on your website defining terms like Zero Trust, Data Loss Prevention, SASE, and XDR in accessible language captures long-tail search traffic from both audiences.
But simplifying jargon does more than improve search visibility. It reduces friction in the buyer journey. When a VP of Marketing can understand your Zero Trust positioning without searching three additional terms, the path from your content to a demo request shortens. Companies that optimize content for both clarity and search performance capture buyers earlier in the research cycle — and hold their attention longer.
Structure these glossary entries as standalone definition pages, each targeting a specific keyword. Use the "X is Y" format in the first sentence of every entry: "Zero Trust Architecture (ZTA) is a security model that requires strict identity verification for every user and device attempting to access resources, regardless of their location relative to the network perimeter." This format is precisely what AI search engines extract for generated answers.
2. Why Does Threat-Responsive Content Outperform Static SEO Strategies?
The cybersecurity threat landscape shifts weekly. The Verizon 2025 Data Breach Investigations Report analyzed over 22,000 incidents and found that vulnerability exploitation as an initial attack vector grew 34% year-over-year, with ransomware now present in 44% of all breaches. These aren't just statistics for your security team, they're content opportunities that drive both search rankings and buyer engagement.
When a new vulnerability or breach makes headlines, cybersecurity buyers actively search for analysis, mitigation steps, and vendor recommendations. Companies that publish informed, technical analysis within days of a major incident capture high-intent search traffic that directly converts. The key is connecting threat intelligence to your product capabilities without making it feel like a sales pitch.
Build an editorial calendar that maps content to both scheduled threat reports (Verizon DBIR, Mandiant M-Trends, CrowdStrike Global Threat Report) and breaking incidents. This gives your SEO program both a stable publishing cadence and the flexibility to produce timely content that competitors haven't optimized for yet.
Understanding how AI search is reshaping buyer discovery in cybersecurity is also critical here. AI engines like Google's AI Overviews prioritize recent, well-sourced content which means threat-responsive articles have a structural advantage for AI citation.
3. How Does Regulatory Compliance Content Build SEO Authority and Drive Pipeline?
In cybersecurity, compliance isn't optional and neither is the content that explains it. Your buyers are actively searching for guidance on frameworks like NIST CSF 2.0, SEC cybersecurity disclosure rules, GDPR data protection requirements, and HIPAA compliance for healthcare security. This content sits at the intersection of high search volume and high buyer intent.
Compliance-focused content builds SEO authority because it naturally attracts backlinks from industry publications, legal resources, and government references. Google's E-E-A-T framework rewards content that demonstrates expertise in regulated domains and cybersecurity regulation is one of the most scrutinized areas in search quality evaluation.
But the real conversion value is this: someone searching "NIST CSF 2.0 compliance checklist for SaaS" isn't casually browsing. They have a budget, a deadline, and a problem. Mapping this content to a compliance assessment CTA converts information-seekers into qualified pipeline. Every compliance article should end with a clear next step whether that's a downloadable assessment, a consultation booking, or a product-specific compliance guide.
Create content hubs organized by regulation. A NIST hub, a GDPR hub, and a SEC disclosure hub each become topical authority centers that strengthen your entire domain's SEO performance while serving as conversion pathways for buyers at different stages of their compliance journey.
4. How Do You Create Cybersecurity Content That Converts Both Technical and Executive Buyers?
The dual-audience challenge in cybersecurity isn't just a content strategy problem, it's a conversion architecture problem. Technical buyers (CISOs, security architects, SOC analysts) need deep product specs, integration documentation, and threat analysis. Executive buyers (VPs of Marketing, CFOs, board members) need business impact metrics, risk quantification, and ROI projections.
Your site structure should serve both without forcing either audience through irrelevant pages. This means building parallel content tracks: technical deep dives that link to documentation and product pages, and business-impact content that links to case studies and ROI calculators. Internal linking between these tracks ensures search engines understand the topical relationship while allowing each audience to self-select their conversion path.
The companies that master this dual-audience approach see measurable results. Applying enterprise CRO tactics that double B2B SaaS conversions to cybersecurity content means designing conversion flows where the CISO reads the architecture whitepaper and the CFO reads the cost-avoidance analysis and both paths lead to a qualified demo request.
Write every piece of cybersecurity content with a "two-reader test": would a CISO find this technically credible? Would a VP of Marketing understand the business implication? If you can satisfy both, your content earns trust from search engines and buyers simultaneously.
5. What Makes Case Studies the Highest-Converting Content Type in Cybersecurity SEO?
In a market where the average data breach costs $4.88 million according to IBM's Cost of a Data Breach Report 2024, buyers don't convert because they enjoyed your blog. They convert because they believe your company can reduce their risk exposure. Case studies that show how your product prevented or mitigated a real-world attack are the most direct path from content consumption to pipeline.
The best cybersecurity case studies include both the technical prevention method and the business impact cost avoided, downtime prevented, compliance maintained, pipeline protected. Show the CISO the architecture. Show the CFO the savings. This dual-metric approach is what separates cybersecurity content that ranks from cybersecurity content that converts.
Structure your case studies for both search engines and AI citation. Lead with the quantifiable outcome in the H1: "How [Company] Prevented a Ransomware Attack and Saved $2.3M in Potential Breach Costs." Use clear "challenge → approach → result" formatting that AI engines can extract as self-contained passages.
Every case study should link to relevant CRO strategies that boost conversions because the traffic a case study earns from search is only valuable if the page converts readers into demo requests, assessment bookings, or sales conversations.
6. Why Is E-E-A-T the Most Important Ranking Factor for Cybersecurity Websites?
Google classifies cybersecurity content as YMYL (Your Money or Your Life), which means inaccurate information can cause real harm, data breaches, financial losses, regulatory violations. As a result, Google applies its strictest E-E-A-T (Experience, Expertise, Authoritativeness, Trustworthiness) evaluation criteria to cybersecurity websites. Shallow content, unattributed claims, and missing author credentials will not rank regardless of how well you optimize for keywords.
Here's what E-E-A-T means in practice for cybersecurity SEO:
Experience: Content should be written or reviewed by professionals with hands-on cybersecurity experience. Author bios need to show real-world credentials, not generic titles.
Expertise: Every claim needs attribution. Link to NIST frameworks, reference CVE databases, cite vendor-neutral research. The more specific your sourcing, the more Google and AI engines trust your content.
Authoritativeness: Earn backlinks from government agencies (.gov), academic institutions (.edu), and established security publications. Highlight team certifications CISSP, CISM, CCSP on your content pages, not just your About page.
Trustworthiness: HTTPS is table stakes. Beyond that, transparent authorship, clear editorial policies, and visible "last updated" dates signal to both algorithms and human buyers that your content is maintained and reliable.
E-E-A-T isn't just about Google's algorithm it's about buyer confidence. When a CISSP-certified author writes your threat analysis, the "Schedule a Demo" button gets clicked more often. Author credibility reduces the perceived risk of engaging with your company, which directly improves featured snippet performance and conversion rates simultaneously.
About LeadWalnut:
For over a decade, LeadWalnut has been at the forefront of crafting high-performing content for leading cybersecurity enterprises in the US. Our expertise in creating content that not only drives website traffic but also builds a consistent sales pipeline is unmatched.
If you're looking to feature in the coveted snippets for keywords like firewall, malware, and SD-WAN, our team of B2B SEO experts is just a conversation away.
FAQ
What makes SEO different for cybersecurity companies?
Cybersecurity falls under Google's YMYL classification, meaning content quality standards are significantly higher than most B2B verticals. Google applies stricter E-E-A-T evaluation because inaccurate security information can cause real harm — data breaches, financial losses, or compliance violations. Cybersecurity SEO requires verifiable expertise, technical accuracy, and authoritative sourcing, including references to frameworks like NIST and standards bodies, that generic B2B content rarely demands.
How long does cybersecurity SEO take to show results?
Enterprise cybersecurity SEO typically takes 4–6 months to show meaningful ranking improvements and 6–12 months for consistent pipeline impact. The timeline is longer than most verticals because keyword competition is intense, content requires genuine technical depth, and trust signals accumulate over time. Companies that combine SEO with conversion rate optimization see earlier pipeline impact because they convert existing traffic more efficiently while building organic visibility.
What are the most valuable cybersecurity keywords to target?
The highest-value keywords combine technical specificity with buyer intent. Terms like "enterprise endpoint security solutions," "SASE vendor comparison," and "zero trust architecture implementation" attract buyers who are actively evaluating vendors. Pure informational terms like "what is a firewall" drive volume but lower conversion rates. A balanced strategy targets awareness-stage terms for AI overview optimization and decision-stage terms for pipeline generation.
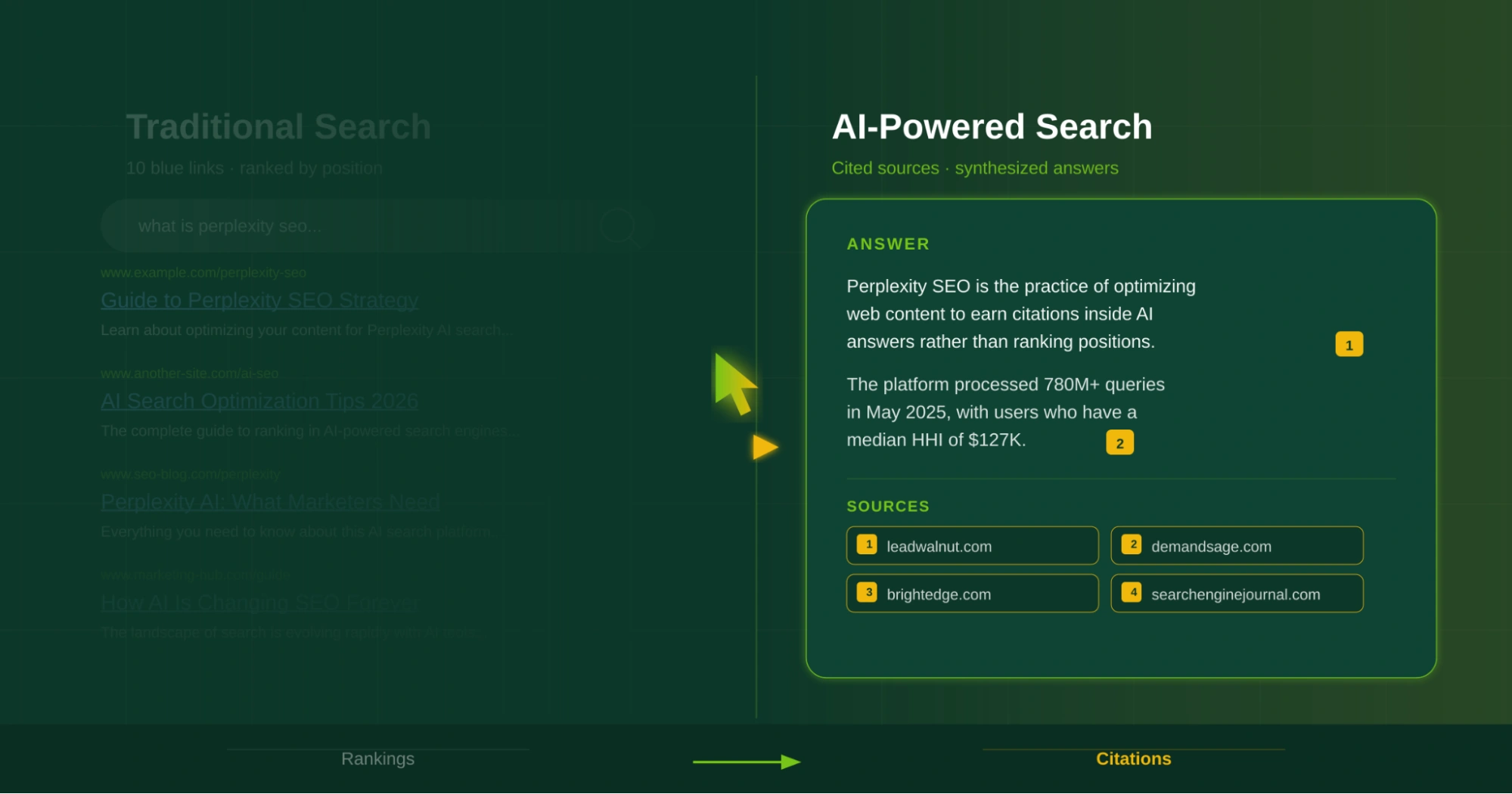
How does AI search affect cybersecurity SEO in 2026?
AI Overviews and answer engines now extract cybersecurity content to answer buyer queries directly in search results. Cybersecurity companies need to structure content for AI extraction — using clear entity definitions, self-contained passages, and FAQ schema — while ensuring their brand gets cited rather than just their information. This means optimizing specifically for AI search engines, not just traditional Google results.
What role does CRO play in cybersecurity SEO strategy?
SEO drives the right buyers to your site. CRO ensures they take action once they arrive. For cybersecurity companies with complex, multi-stakeholder buying cycles, this means optimizing for micro-conversions: whitepaper downloads, compliance assessment requests, and demo bookings. An integrated SEO+CRO approach typically delivers 3–5× higher ROI than either discipline working in isolation, because you improve both the volume and the conversion rate of qualified organic traffic.

Subscribe to our blog

How can LeadWalnut help?
Related Articles

Top 10 B2B SaaS Digital Marketing Agencies to Hire in 2026
.png)
How AI Search Engines Are Rewriting the B2B Lead Generation Playbook